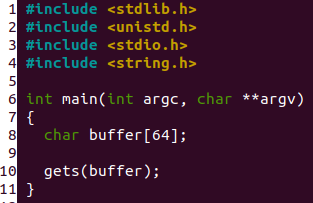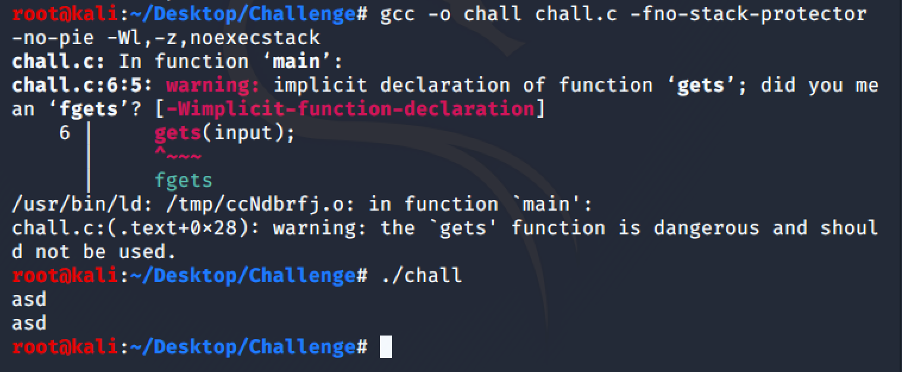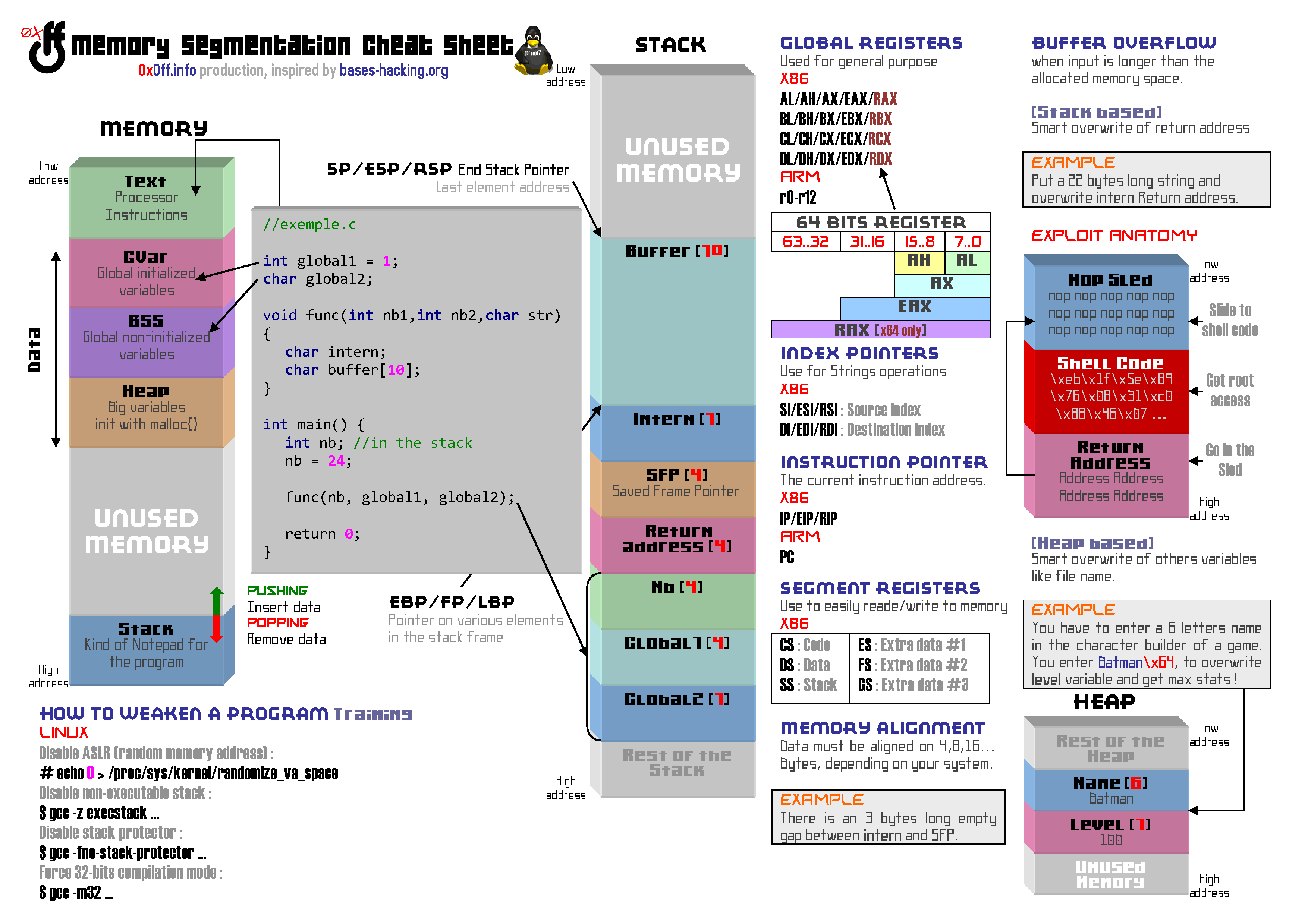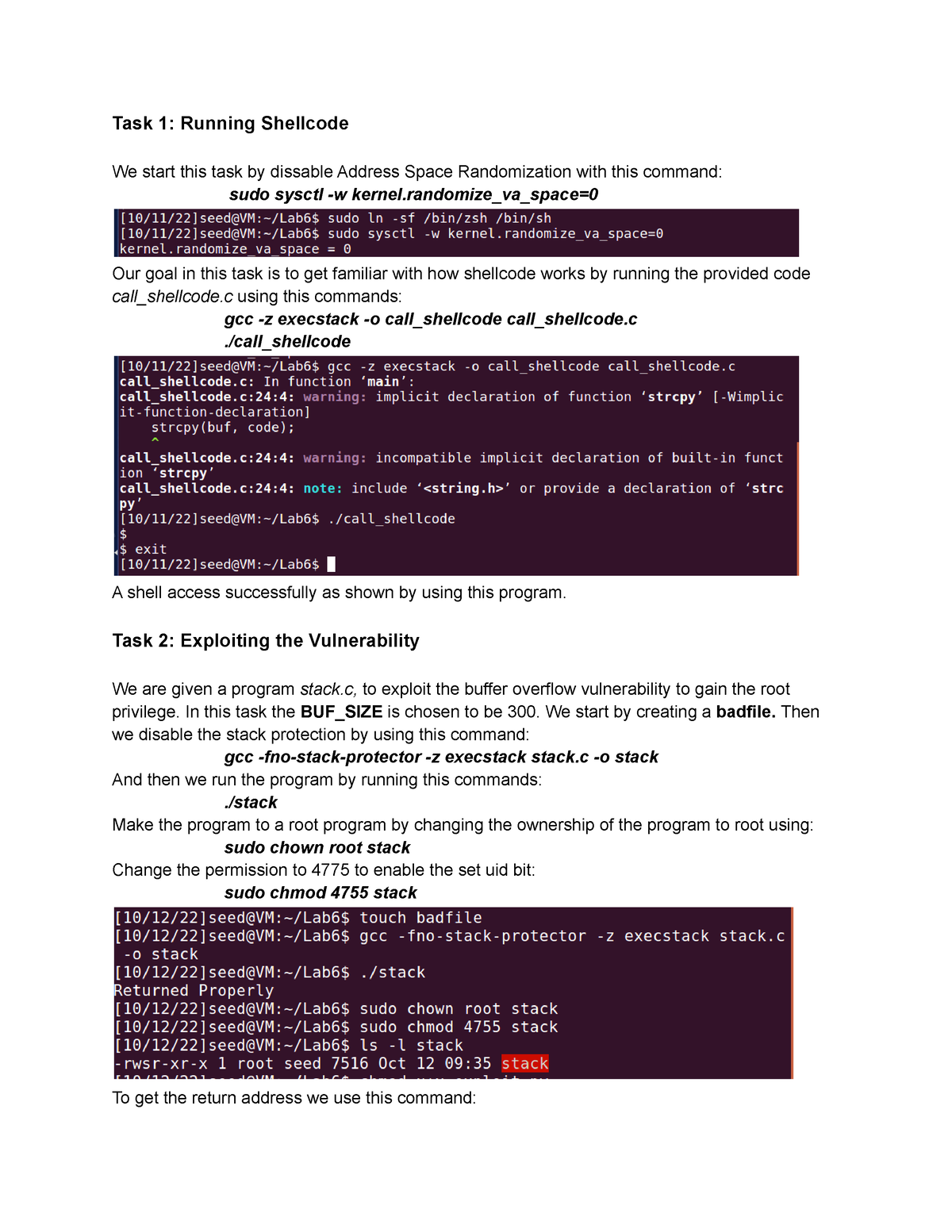
Buffer-Overflow Vulnerability Lab 6 - Task 1: Running Shellcode We start this task by dissable - Studocu

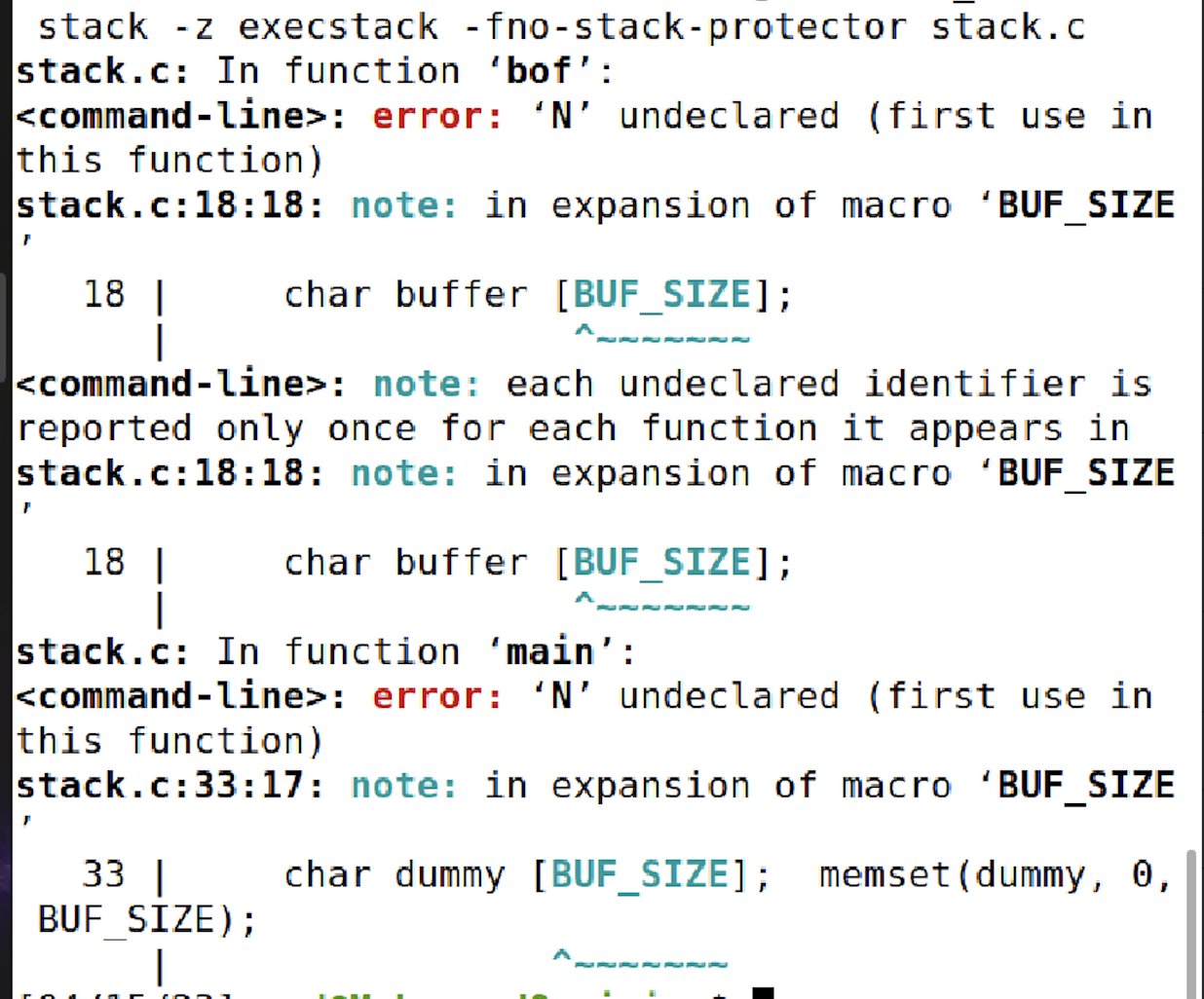
C++ code (TSF.c) Compiling this code using the command 'gcc TSF.c -z... | Download Scientific Diagram
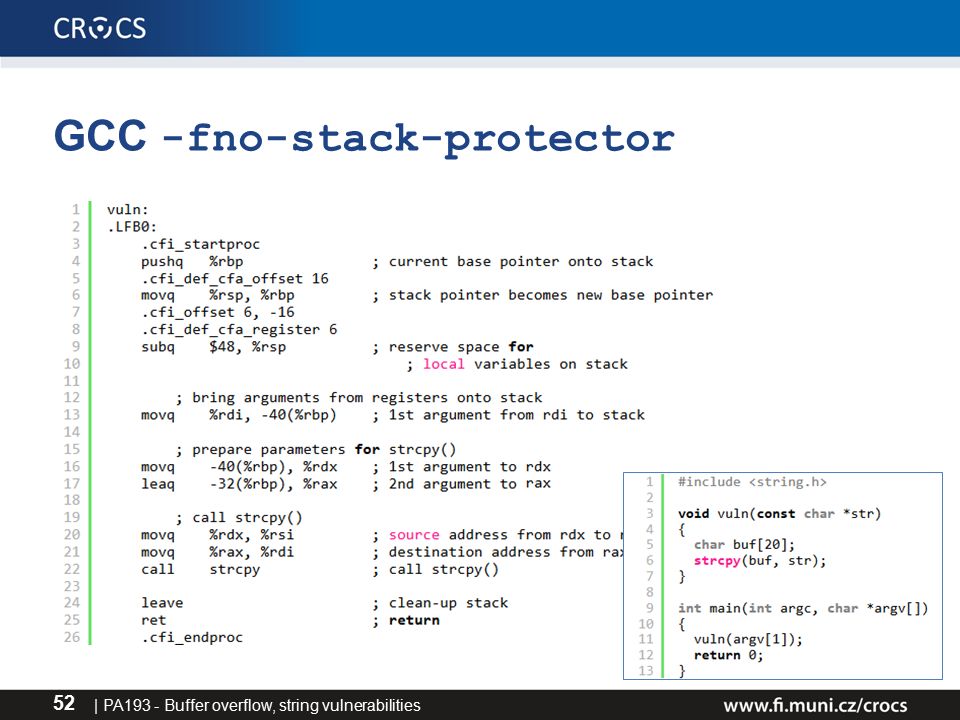
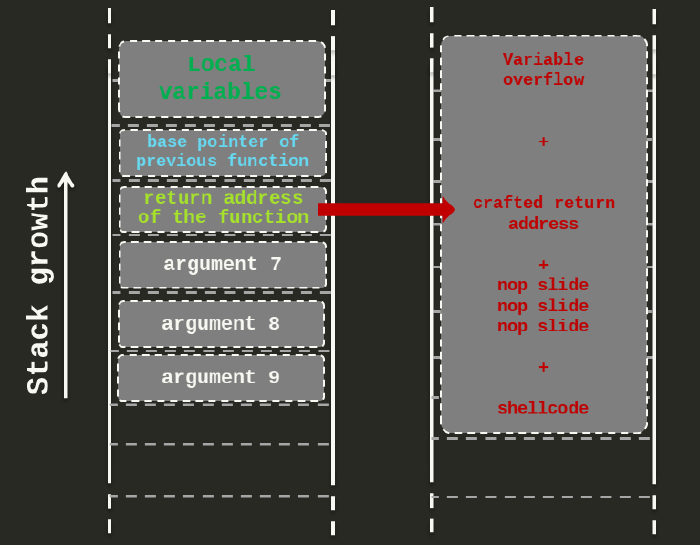
PA193 - Secure coding principles and practices Language level vulnerabilities: Buffer overflow, type overflow, strings Petr Švenda - ppt download

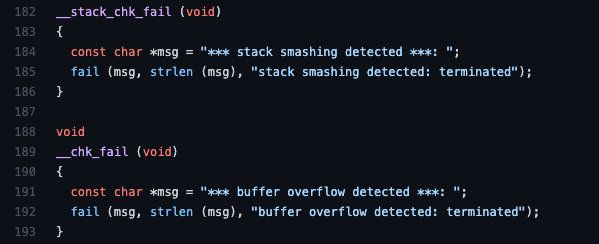
Stack buffer overflow protection 學習筆記– Stack canaries mechanism in User space – SZ Lin with Cybersecurity & Embedded Linux